Today, the first workshop 1st Workshop on Heuristic and Pattern Mining for Multi-Omics Data Analytics was held at IEEE BIBM 2025, online. I co-organize this workshop with M. Saqib Nawaz and other collaborators. The workshop focus on various machine learning and pattern mining methods and their applications to the analysis of multi-omics data.
Here are the slides from the opening ceremony:
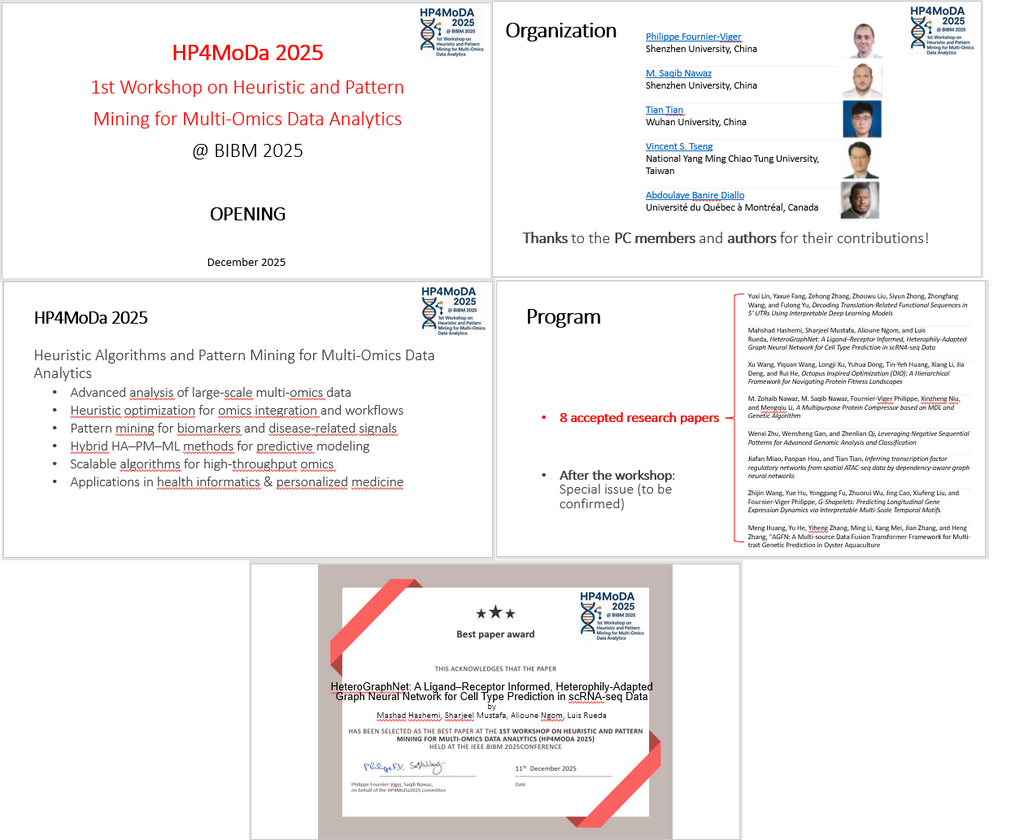
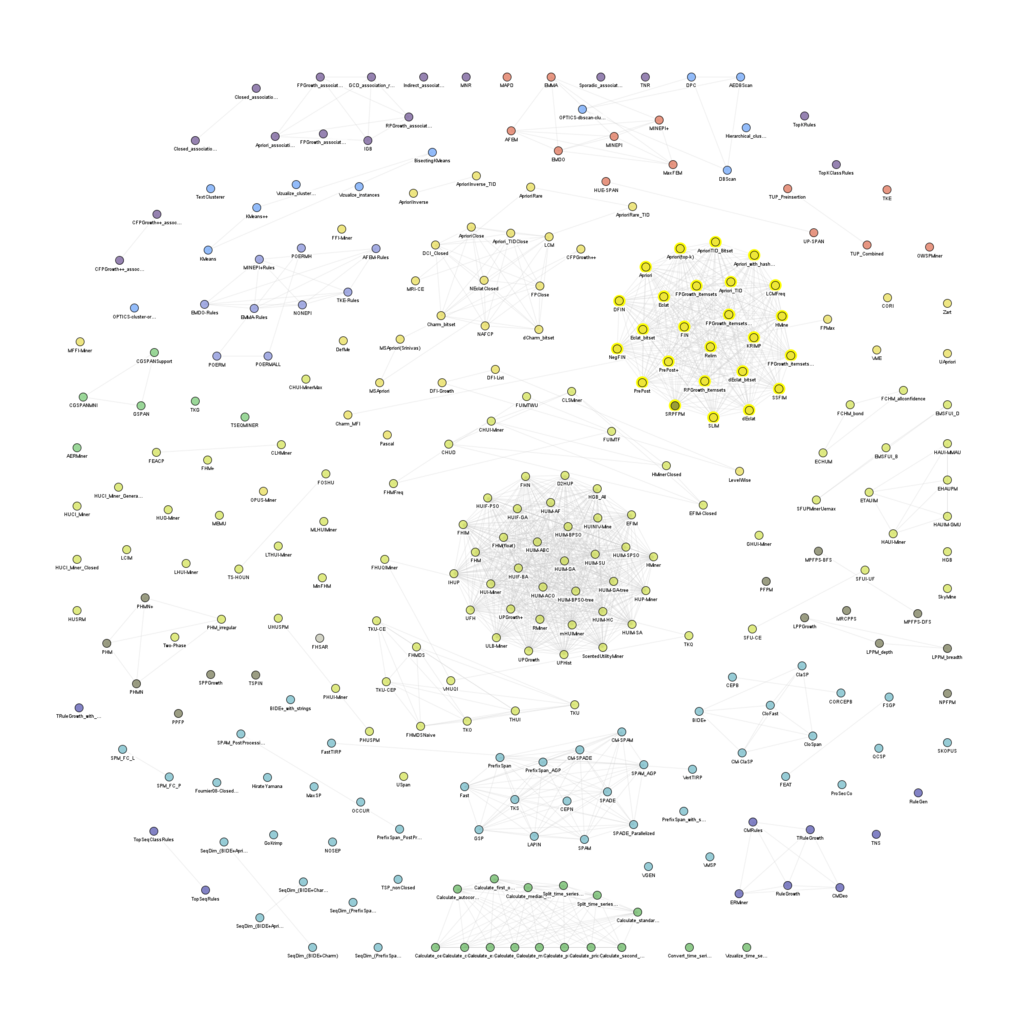
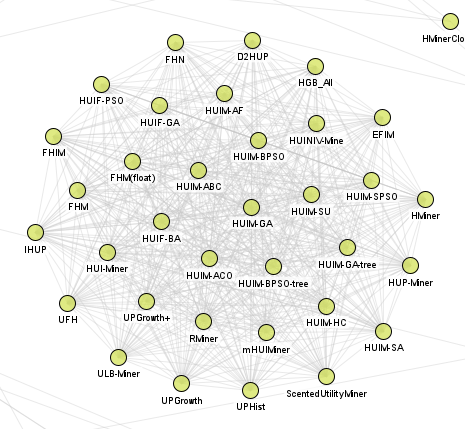
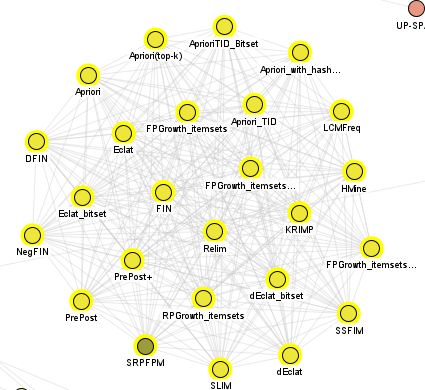
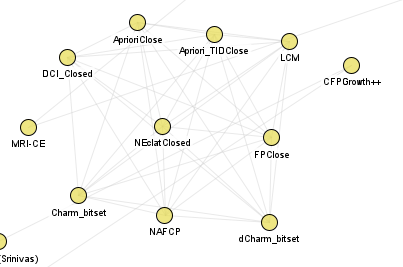
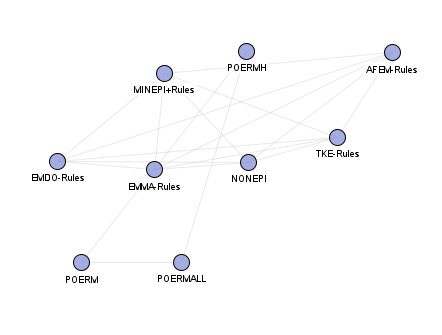
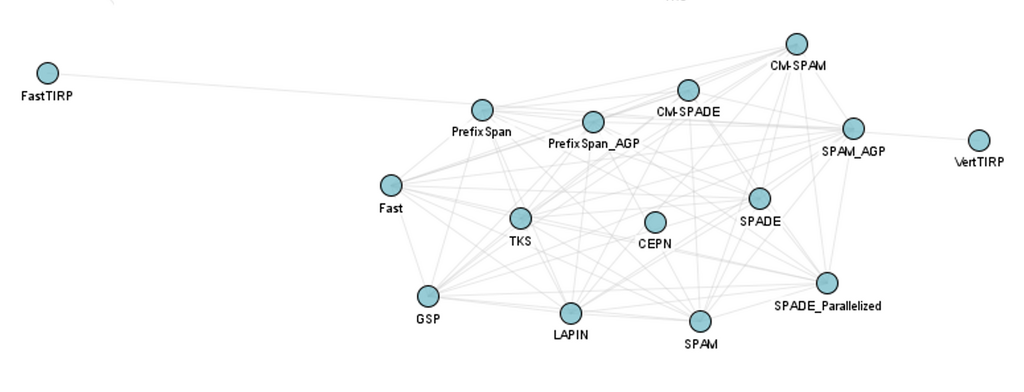
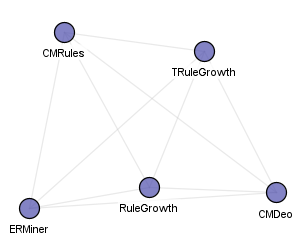
It was announced that 8 papers have been accepted by the workshop this year. They cover multiple topics such as interpretable deep learning for regulatory sequence analysis, graph neural networks for single-cell and spatial omics data, heuristic and bio-inspired optimization for protein fitness landscapes, minimum description length and evolutionary approaches for protein compression, advanced sequential and temporal pattern mining methods, and multi-source data fusion models for predicting complex genetic traits.
We also mentioned that we are currently working to organize a special issue for extensions of the papers (to be confirmed later).
We also announced that the best paper award of the workshop was given to this paper by researchers from Canada:
Mahshad Hashemi, Sharjeel Mustafa, Alioune Ngom, and Luis Rueda, HeteroGraphNet: A Ligand–Receptor Informed, Heterophily-Adapted Graph Neural Network for Cell Type Prediction in scRNA-seq Data
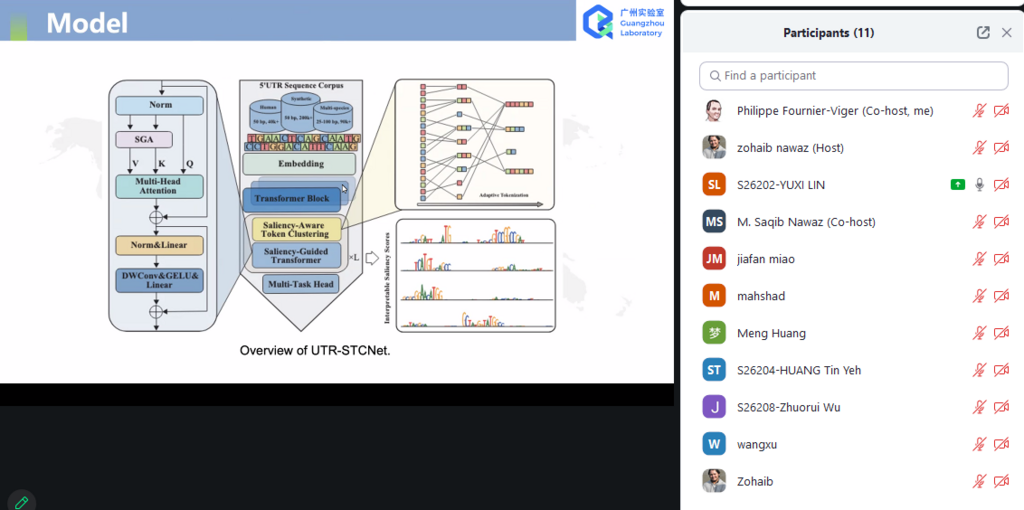
There was several interesting presentations on diverse topics. Here for example, a screenshot from the first paper presentation by Lin, Yuexi et al. about Decoding Translation-Related Functional Sequences in 5’ UTRs Using Interpretable Deep Learning Models:
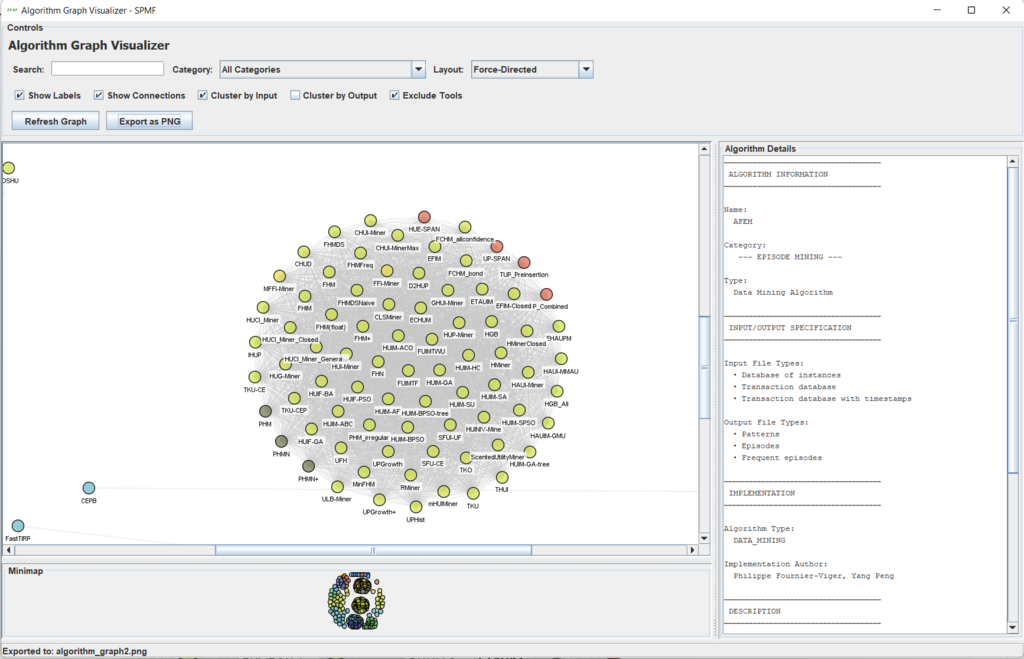
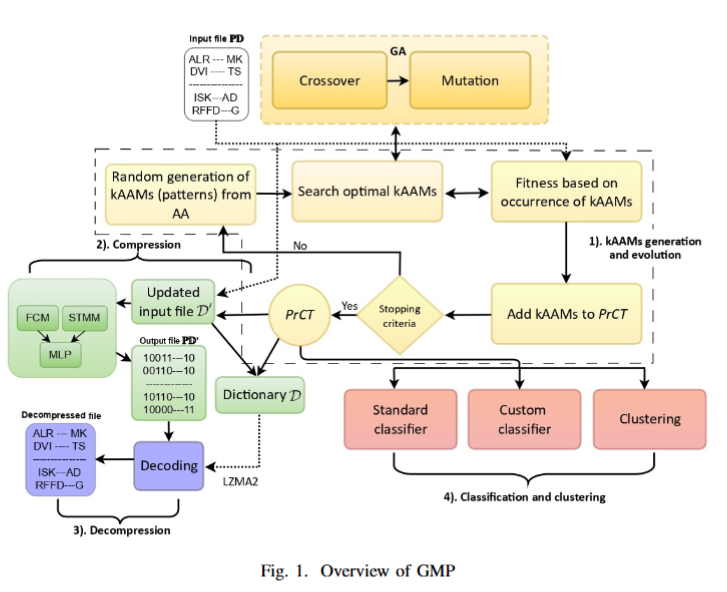
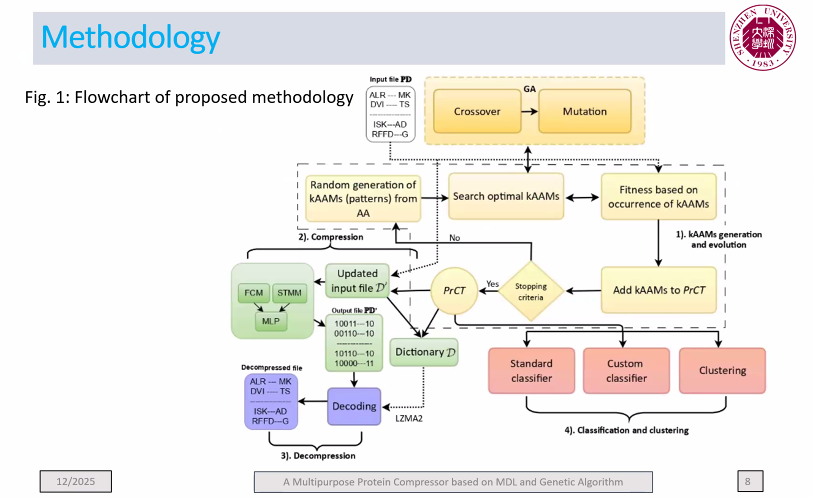
Among the papers, my PhD student presented a new algorithm called GMP for protein sequence compression based on pattern mining. Here are a few slides to show an overview:
This is just a short report about the workshop. It has been a success for the first edition of this workshop. We thus plan to organize it again next year!